Internet Tools
Tools for Web, Networking, and the Internet
This collection covers a broad range of tools useful for web developers, network engineers, students, and anyone working with internet technologies — from encoding utilities to IP address planning.
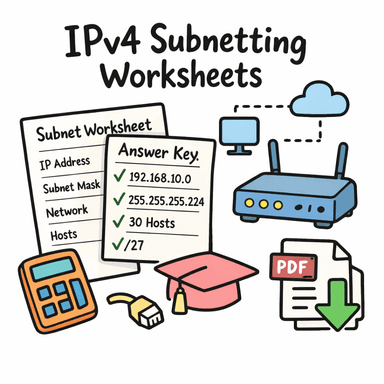
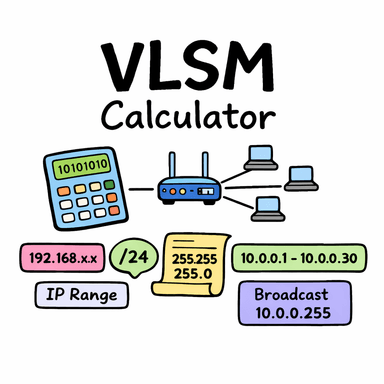
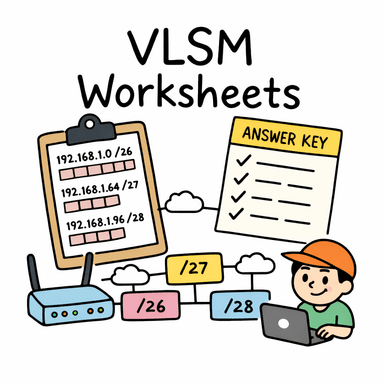
IP Subnetting and VLSM
Understanding how IP address spaces are divided is a fundamental networking skill. The subnetting tools on this page let you work through IPv4 subnet calculations and VLSM (Variable Length Subnet Masking) problems interactively.
VLSM allows different subnets within the same network to have different sizes, making efficient use of available address space rather than dividing it into equal blocks. It is the basis of classless inter-domain routing (CIDR) and modern network design.
The IPv4 subnetting worksheet generator creates printable practice problems for students learning subnetting, and the VLSM calculator walks through the allocation process step by step.
Password Generation
Strong passwords are long, random, and unique. The password generator on this page creates cryptographically random
passwords using the browser's crypto.getRandomValues() API — the same source of randomness used in
secure applications. Generated passwords are never transmitted or stored anywhere.
A strong password for a typical account should be at least 16 characters long and include a mix of uppercase, lowercase, digits, and symbols. For most people, a password manager that generates and stores unique passwords is more practical than memorising them.
Base64 Encoding
Base64 is commonly encountered in web development contexts: data URIs for embedded images, HTTP Basic Authentication headers, JWT tokens, and API responses that carry binary data. The Base64 encode and decode tools on this page process text instantly in the browser.
Data URIs
A data URI embeds a file's content directly in a URL using Base64 encoding. The format
data:image/png;base64,... can be used anywhere a URL is expected — in <img src>, CSS
background-image, and other attributes — without a separate network request. The data URI generator
tool builds these strings from uploaded files.
Frequently Asked Questions
- What is CIDR notation?
- CIDR (Classless Inter-Domain Routing) notation expresses an IP address and its associated network mask as a
single string, like
192.168.1.0/24. The number after the slash is the prefix length — the count of fixed bits in the network portion of the address./24means 24 fixed bits, leaving 8 bits for host addresses (256 total, 254 usable). - What is the difference between a subnet mask and CIDR prefix?
- They represent the same information in different formats. The subnet mask
255.255.255.0is the dotted-decimal form;/24is the CIDR prefix form. Both indicate that the first 24 bits identify the network and the remaining 8 bits identify hosts within it. - What makes a password cryptographically strong?
- Cryptographic strength comes from true randomness and sufficient length. A password generated by
crypto.getRandomValues()is as random as modern hardware allows. Length matters enormously — each additional character multiplies the number of possible passwords. 16 random characters from a 72-character set produces over 10²⁹ possible passwords — far beyond practical brute-force attack.