Hash & Encryption Text Tools
Hashing vs. Encryption vs. Encoding
These three terms are often confused but refer to very different operations:
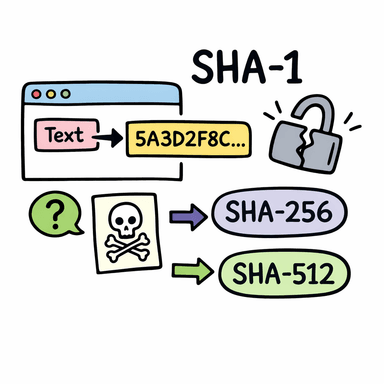
- Hashing is a one-way transformation. You pass text into a hash function and receive a fixed-length digest (a string of hexadecimal characters). The same input always produces the same output, but you cannot reverse the process to recover the original text. Hashing is used to verify data integrity and to store passwords securely without saving the password itself.
- Encryption is a two-way transformation. Data is scrambled using a key, and anyone with the correct key can reverse the process to recover the original data. The classical ciphers on this page (Caesar cipher, transposition cipher) are simple historical examples of encryption.
- Encoding is a format transformation with no security intent. Base64 encoding converts binary data into a text-safe representation. It is not encryption — Base64-encoded data can be decoded by anyone instantly. Its purpose is to safely carry binary data through systems that only handle text.
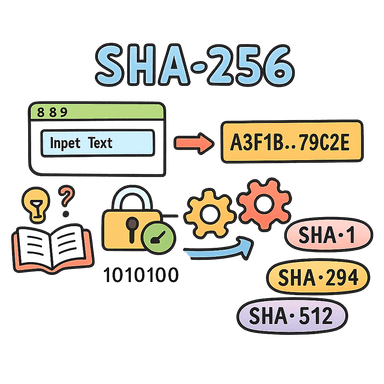
SHA Hash Functions
SHA (Secure Hash Algorithm) is a family of cryptographic hash functions published by NIST. The tools on this page cover the most commonly used variants:
| Function | Output length | Common uses |
|---|---|---|
| SHA-1 | 160 bits (40 hex chars) | Legacy systems, Git commit IDs (being phased out) |
| SHA-256 | 256 bits (64 hex chars) | Password storage, digital signatures, file verification |
| SHA-384 | 384 bits (96 hex chars) | TLS certificates, higher-security applications |
| SHA-512 | 512 bits (128 hex chars) | High-security hashing, when collision resistance is critical |
SHA-1 is considered cryptographically broken for security-sensitive uses — chosen-prefix collisions have been demonstrated. For new applications, use SHA-256 or higher.
Base64 Encoding and Decoding
Base64 represents binary data using 64 printable ASCII characters (A–Z, a–z, 0–9, +, /). It was designed to transmit binary data through channels that only handle text — for example, embedding images in HTML or CSS as data URIs, or encoding binary attachments in emails.
Base64 increases data size by approximately 33%. It is not compression and not encryption. Any Base64 string can be instantly decoded by anyone.
Common Base64 applications include embedding images as data URIs (data:image/png;base64,...), encoding
API credentials in HTTP Basic Authentication headers, and representing binary data in JSON payloads.
Classical Ciphers
The Caesar cipher and transposition cipher are simple historical encryption methods, useful for teaching concepts but not suitable for any real security use.
The Caesar cipher shifts each letter in the alphabet by a fixed number of positions. With a shift of 3, A becomes D, B becomes E, and so on. It was used by Julius Caesar for military correspondence. It can be broken trivially by trying all 25 possible shifts (brute force) or by frequency analysis.
The transposition cipher rearranges the characters in a message according to a key, rather than substituting them. The letters themselves are unchanged but their positions are shuffled. Transposition ciphers are more complex than substitution ciphers but are still easily broken with modern analysis.
Frequently Asked Questions
- Can I reverse a SHA hash to get the original text?
- No. SHA is a one-way function by design — reversing it is computationally infeasible for a properly complex input. However, simple or common inputs (like dictionary words or short passwords) can be found by looking them up in pre-computed rainbow tables. For secure password storage, always use a password-specific hashing function like bcrypt, scrypt, or Argon2 rather than raw SHA.
- Is SHA-256 safe to use in 2026?
- Yes. SHA-256 remains cryptographically strong and is widely used in TLS, code signing, and password hashing. There are no known practical attacks against it.